No Username or Password… No Wishes!
By Theon Alleyne, CRCP, CCEP , USA Senior Managing Consultant,IBM
Apparently 8.4 Billion passwords were revealed on a hacker forum. The implications are endless. Attackers can simply conduct Brute Force tactics to compromise reused passwords on different sites. Reputable data leak checkers like “Have I Been Pwned” can help, but a better course of action is utilizing a combination of a strong password or a password manager. CyberNews
𝐌𝐢𝐧𝐝 𝐭𝐡𝐞 𝐏assword
There are a lot of challenges that come with managing passwords.
The matter is critical for network access in organizations.
Why?
As I said before, the human is the weakest link in the cyber security chain. The good news is that there is no host delightfully saying “Good Bye”.
With so many accounts to log into, password fatigue sets in quickly. It is important to resist the urge to use common, easy to remember passwords, across multiple sites.
I understand that it reduces stress, but the consequences and cost may go well beyond $1 million.
Here are some actions you can take to protect your company’s devices or accounts from unauthorized access.
⛔️ Don’t write down your passwords on a paper very close to the device you work on.
⛔️ Don’t use the same passwords across multiple platforms.
➕Add complex words to your passwords.
➕Use passwords managers to record your passwords so you have to think too much to recall them.
𝟎𝐩𝐞𝐧 Sesame !
James Howells, a British IT worker, and Stephan Thomas from San Francisco, wish they could say Open Sesame to get back their fortunes.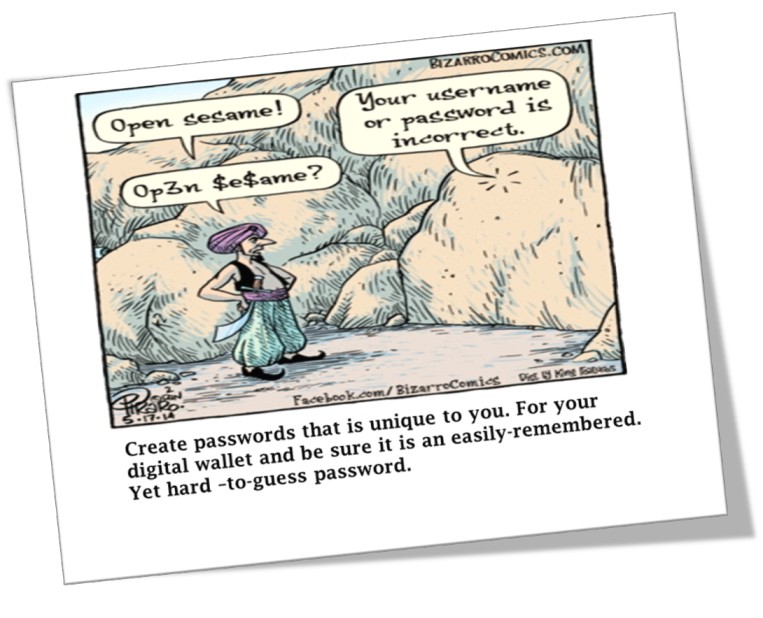
Thomas has his fortune in a Bitcoin wallet that holds 7,002 Bitcoin, but he can’t remember the password.
Howells believes his 7,500 bitcoins are on a hard drive in a UK landfill and wants permission to open up the rubbish heap so he can try a different type of mining.
Together almost half a billion dollars is at stake.
Both of these situations speak to the need for exchanges that can hold digital keys securely, and withstand attacks.
Thomas claims he lost the paper where he wrote down the passwords for his IronKey.
IronKey is like a Genie that grants ten wishes/guesses, before going poof! Thomas has two guesses left.
Here are two keys to keep in mind, to secure your digital wallet.
First, enable passwords on your digital device before use, and apply the layers of security provided by the device.
Second, create a password that is unique to you, for your digital wallet, and be sure it is an easily- remembered, yet hard-to-guess password.
Most important, don’t lose your device or password.
Bad passwords
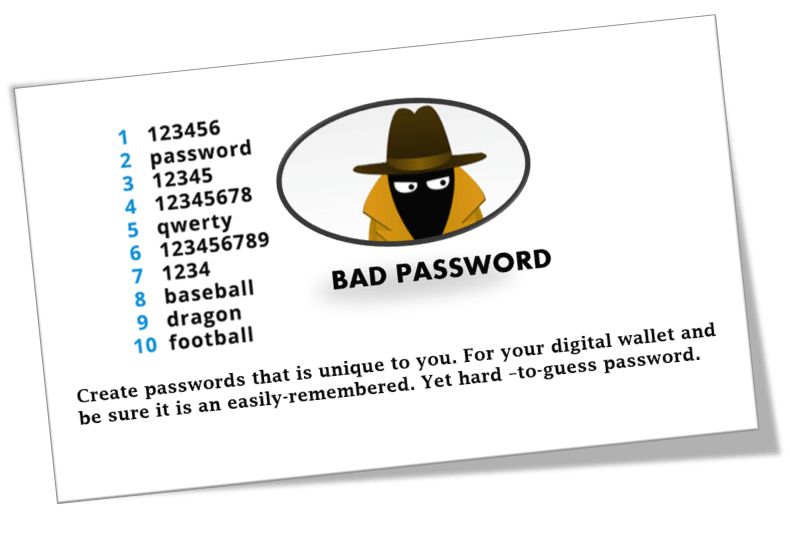
Haven’t you learnt anything about using “123456” as passwords?
It is terrible how people ignore good advice.
Password Manager, NordPass reported that a staggering 2.5million number of people still use “123456” as their passwords this year.
If it is way for you, it’s super easy for the bad actors.
The UK National Cyber Security survey in 2019 revealed that 23.2 million people still use “123456” as their passwords, 7.7 million people use “123456789” and 3.6 million people use “password” as their passwords.
We can do better than allowing the bad actors to crack our passwords.
When you want to create strong passwords, avoid using names of football clubs, musicians, dictionary words, number combinations, fictional characters, strings of adjacent keyboard, repetitive characters, your date of birth, phone number or name.
Instead use a combination of upper and lower- case letters including numbers and symbols, make it longer to up to 12 characters or more and never reuse passwords across multiple accounts.
Do you know anyone with an easy password?
𝐀𝐫𝐞 𝐲𝐨𝐮𝐫 𝐞𝐠𝐠𝐬 𝐢𝐧 𝐨𝐧𝐞 𝐜𝐲𝐛𝐞𝐫𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐛𝐚𝐬𝐤𝐞𝐭?
Bad actors just place our Facebook account details on the open market for FREE.
Yes, this is the information you had to give Facebook to get an account. And n
ow it’s
all up for grabs … phone numbers, Facebook IDs, full names, locations, birthdates, bios, and maybe, email addresses.
Here are three quick things to consider to protect yourself from fraud and cyber threats.
1. Create a social media email address that is different from your personal or business email.
2. Where possible use a free web phone number like Google Voice for your Social Media account.
3. Change your Social Media password every time you change your business password.
𝗗𝗶𝘀𝗮𝗯𝗹𝗲 𝗱𝗲𝗳𝘂𝗻𝗰𝘁 𝗮𝗰𝗰𝗼𝘂𝗻𝘁𝘀….
The recent hack into Colonial Pipeline Co. “Colonial” is a clear example of why multi-factor authentication must be used to protect online access.
multi-factor authentication must be used to protect online access.
Investigations into the attack revealed that the hackers gained entry into the network through a virtual private network “vpn” account. VPN’s allows employees to remotely access the company’s computer network.
Interestingly, the hackers used a defunct account that was not disabled.
Further, investigators noted that password a for the inactive account was also discovered in a batch of leaked passwords on the dark web.
What this means is that, an employee may have used the same password on another account that was previously hacked.
The good news is that US Government has recovered more than half of the of $4.4 million ransom Colonial paid to regain access to it’s network.
Colonial was fortunate.
What would happen to the reputation of your financial institution, if it was hacked?
𝗦𝘁𝗼𝗽 𝗴𝗿𝗮𝗻𝘁𝗶𝗻𝗴 𝗮𝗽𝗽𝘀 𝗽𝗲𝗿𝗺𝗶𝘀𝘀𝗶𝗼𝗻 to use accessibility services.

Yes, write it down. ✍️
Always deny requests for accessibility services.
Do you know that any app approved for accessibility services to your device, can take over your device? 🧐
Which means the game you downloaded can cause the funds in your bank account to disappear. Poof! 💨 🥲
Also of note…..
Mobile security analysts been found apps on both Google and Apple stores claiming to be helpful utilities, that can scan your device and tell you when updates to chrome, WhatsApp, PDF reader or other apps are available.
In fact, McAfee research revealed that these apps are used to install fake updates that take over a smartphone or tablet and download malware in order to steal the user’s bank account passwords. 🏦
So, before downloading apps, research the developer’s information to see if you find online complaints.
An app available on Google or Apple stores does not mean it is 100% safe.
- Phishing is not done at sea - April 13, 2023
- No Username or Password… No Wishes! - April 13, 2023
- Compliance is Not the “Bogeyman” - January 28, 2021


Stay connected